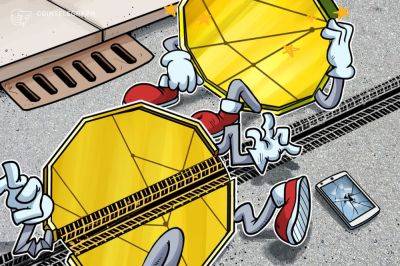
Curve Finance pools exploited in over $24M due to reentrancy vulnerability
Several stable pools on Curve Finance using Vyper were exploited on July 30, with losses reaching $24 million at the time of writing. According to Vyper, its 0.2.15, 0.2.16 and 0.3.0 versions are vulnerable to malfunctioning reentrancy locks.
"The investigation is ongoing but any project relying on these versions should immediately reach out to us," Vyper wrote on X.
We're running a large white hat rescue operation. Please reach out if you think you're affected as a project. https://t.co/tssWcRHg35
According to initial investigation, some versions of the Vyper compiler do not correctly implement the reentrancy guard, which prevents multiple functions from being executed at the same time by locking a contract. Reentrancy attacks can potentially drain all funds from a contract.
A number of decentralized finance projects were affected by the attack. Decentralized exchange Ellipsis reported that a small number of stable pools with BNB were exploited using an old Vyper compiler. Alchemix also witnessed $13.6 million outflow, along with $11.4 million exploited on JPEGd’s.
Certain type of Curve factory pool is encountering read-only reentrancy attack and causing a total loss of $11m(@JPEGd_69) + $13m(@AlchemixFi) + ...Initial investigation founds that vyper compiler (0.2.15) doesn't implement the reentrancy guard correctly. add_liquidity and… pic.twitter.com/avaHdtSFsm
The exploit sparked panic across the DeFi ecosystem, prompting a wave of transactions across pools and a rescue operation from white hats. Data from CoinMarketCap shows Curve Finance's utility token Curve DAO (CRV) declining over 5% in reaction to the news. CRV's liquidity has declined significantly in recent months, making it vulnerable to violent price swings,
Read more on cointelegraph.com